Breach Of Contract Law Dictionary Line Icon Vector Illustration Stock Illustration - Download Image Now - iStock

We only got half of the Security Breach. Vanessa was supposed to be a playable character. S.T.A.F.F bots were supposed to have voice lines. Sewer family had Voice lines too. "I always
Cyber attack pixel perfect white linear icon for dark theme. Deploy malware. Hacking activity. Data breach. Thin line illustration. Isolated symbol for night mode. Editable stroke. 12863344 Vector Art at Vecteezy
Lock Breach Line Icon, Privacy and Protect, Padlock Sign, Vector Graphics, a Linear Pattern on a White Background. Stock Vector - Illustration of firewall, outline: 142729375

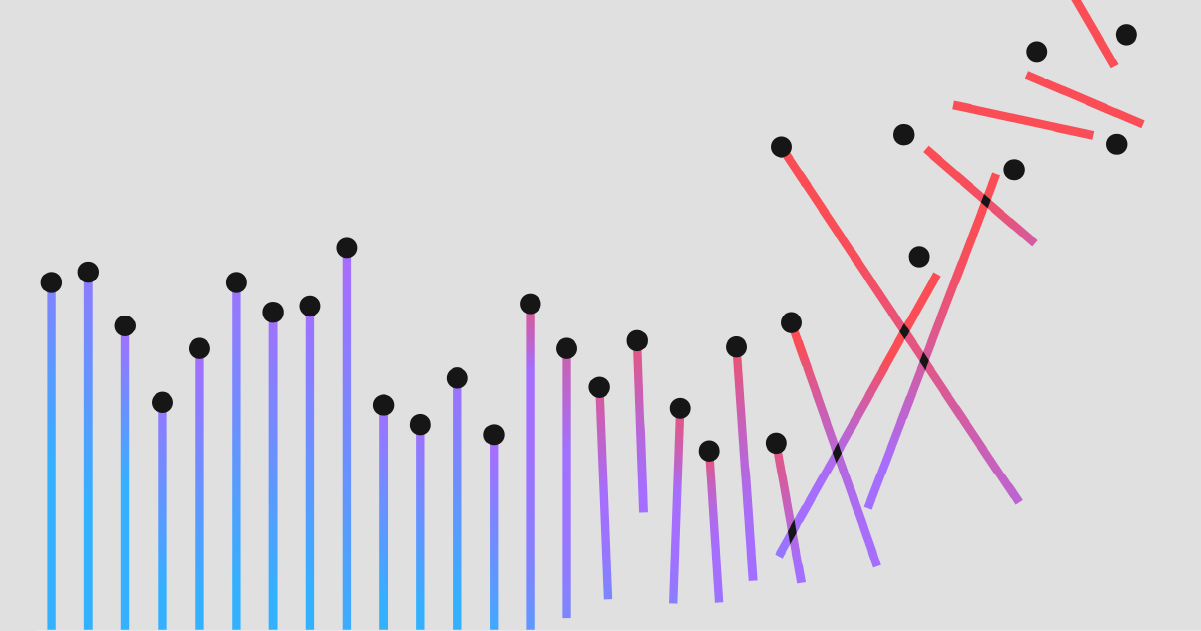
What's the Line Between a Security Breach, and a Data Breach? - DLC Technology Blog | DLC Technology

/cdn.vox-cdn.com/uploads/chorus_asset/file/19887730/Breach_E_full_charge.jpg)












